 01 Specimen
01 Specimen Data extraction at scale
Large-scale crawlers built to harvest catalogues, prices, and competitive intelligence without respecting platform limits.
Bots, Labs & Sandboxes
Map bot variants, follow guided lab tracks, and test defensive tradeoffs in safe sandboxes built for defenders.
Bots · BLS-01
Each family has different economics, infrastructure, evasion habits, and evidence. The bot map gives you the lay of the land before the lab work begins.
 01 Specimen
01 Specimen Large-scale crawlers built to harvest catalogues, prices, and competitive intelligence without respecting platform limits.
 02 Specimen
02 Specimen Credential testing systems that turn leaked usernames and passwords into account takeover pressure.
 03 Specimen
03 Specimen Inventory and checkout automation built to reserve stock, win queues, and bypass purchase limits.
 04 Specimen
04 Specimen Account farms and posting systems that flood reviews, comments, and social surfaces past moderation.
 05 Specimen
05 Specimen Synthetic content operations combining agents, templates, and feedback loops to produce material at industrial scale.
 06 Specimen
06 Specimen Anti-detect browser profiles tuned to look ordinary while still leaking contradictions under pressure.
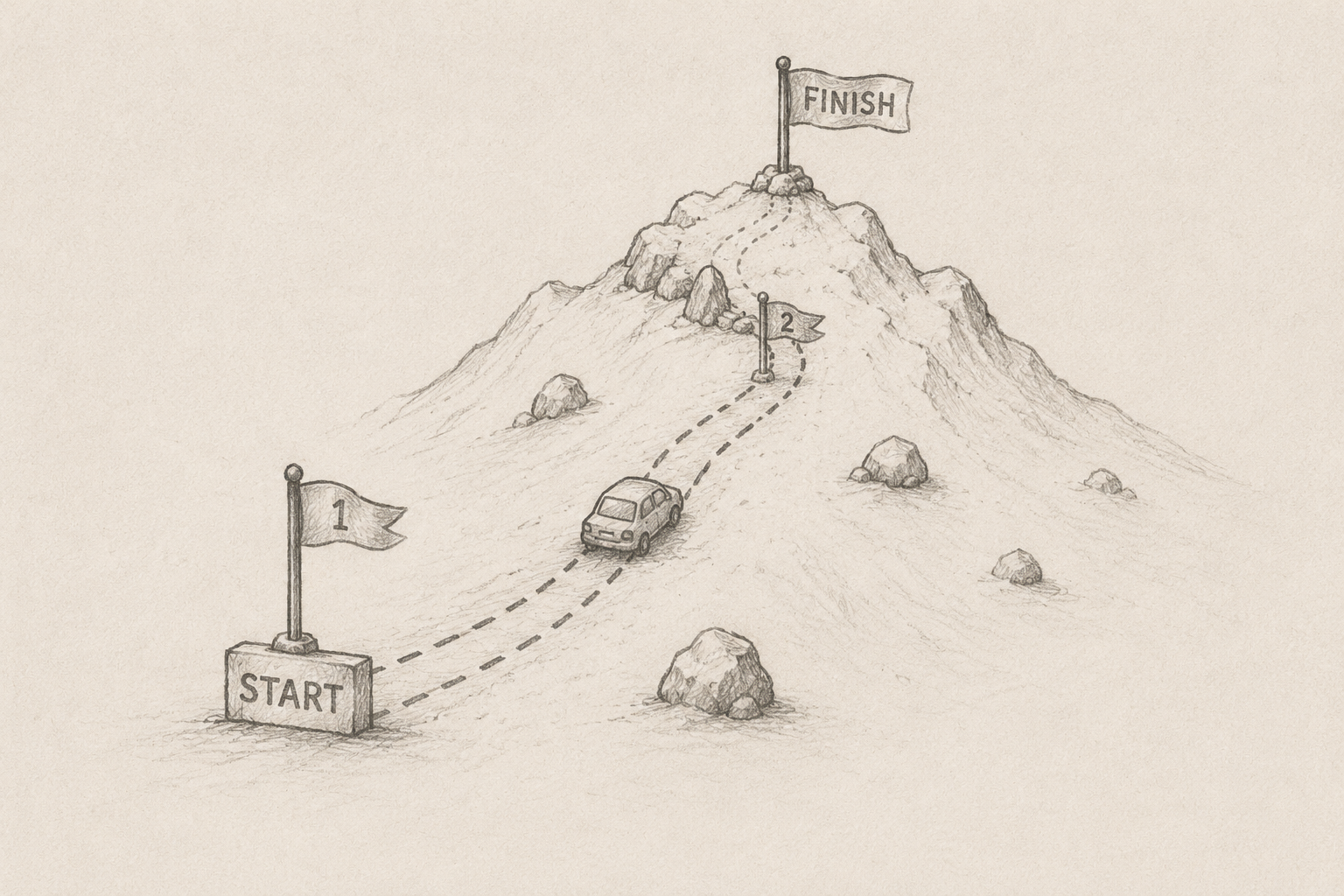
Lab Tracks · BLS-02
The labs work the bot-defense stack one layer at a time — from the device underneath the request up to the business cost it lands on. Each layer turns a problem into evidence: a collector, detector, scoring module, or runbook.
Track 01 / 08 Layer I
Read the device underneath the browser. Clock drift, GPU rendering quirks, sensor noise, and display geometry rarely fake themselves coherently — that incoherence is your first signal.
Track 02 / 08 Layer II
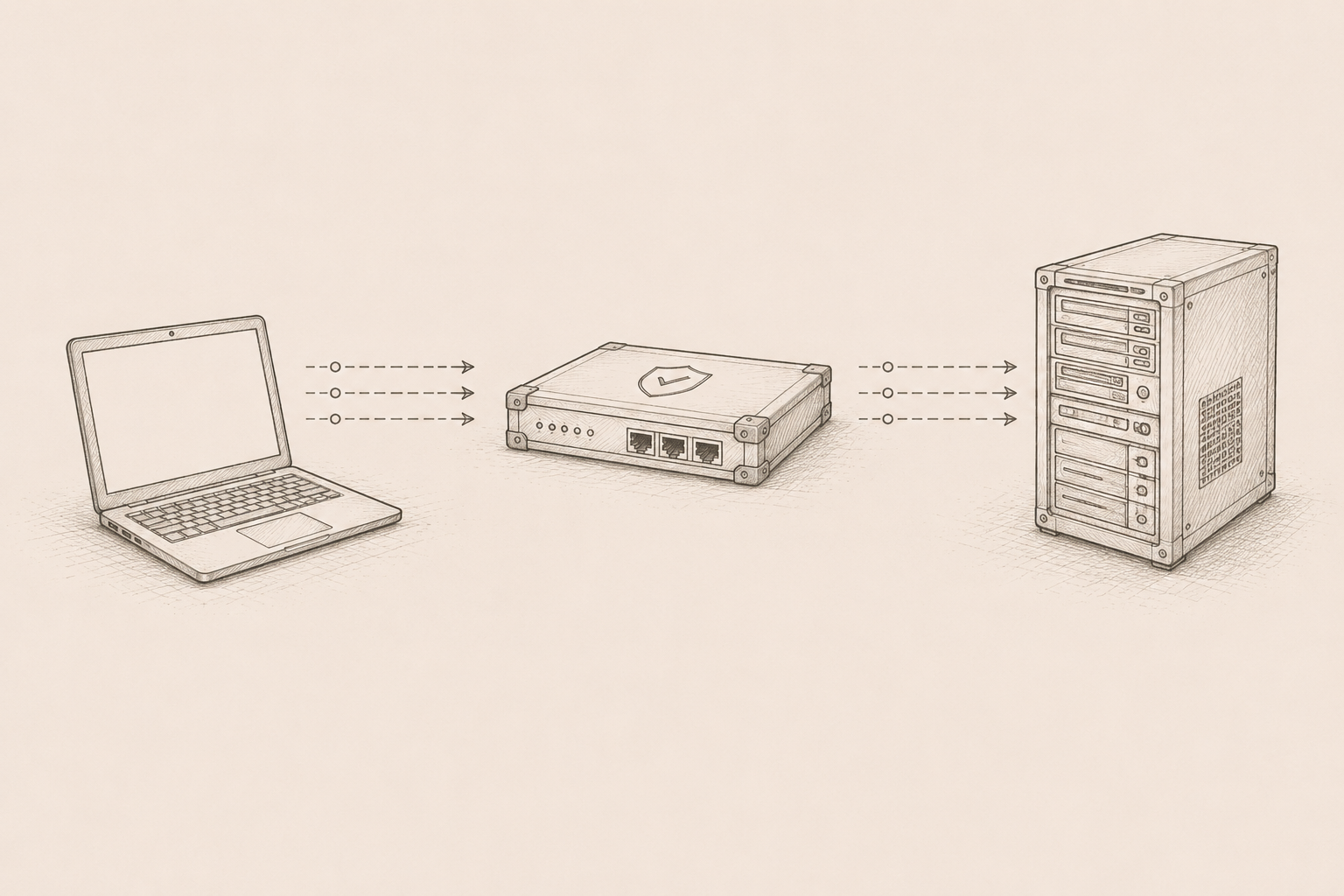
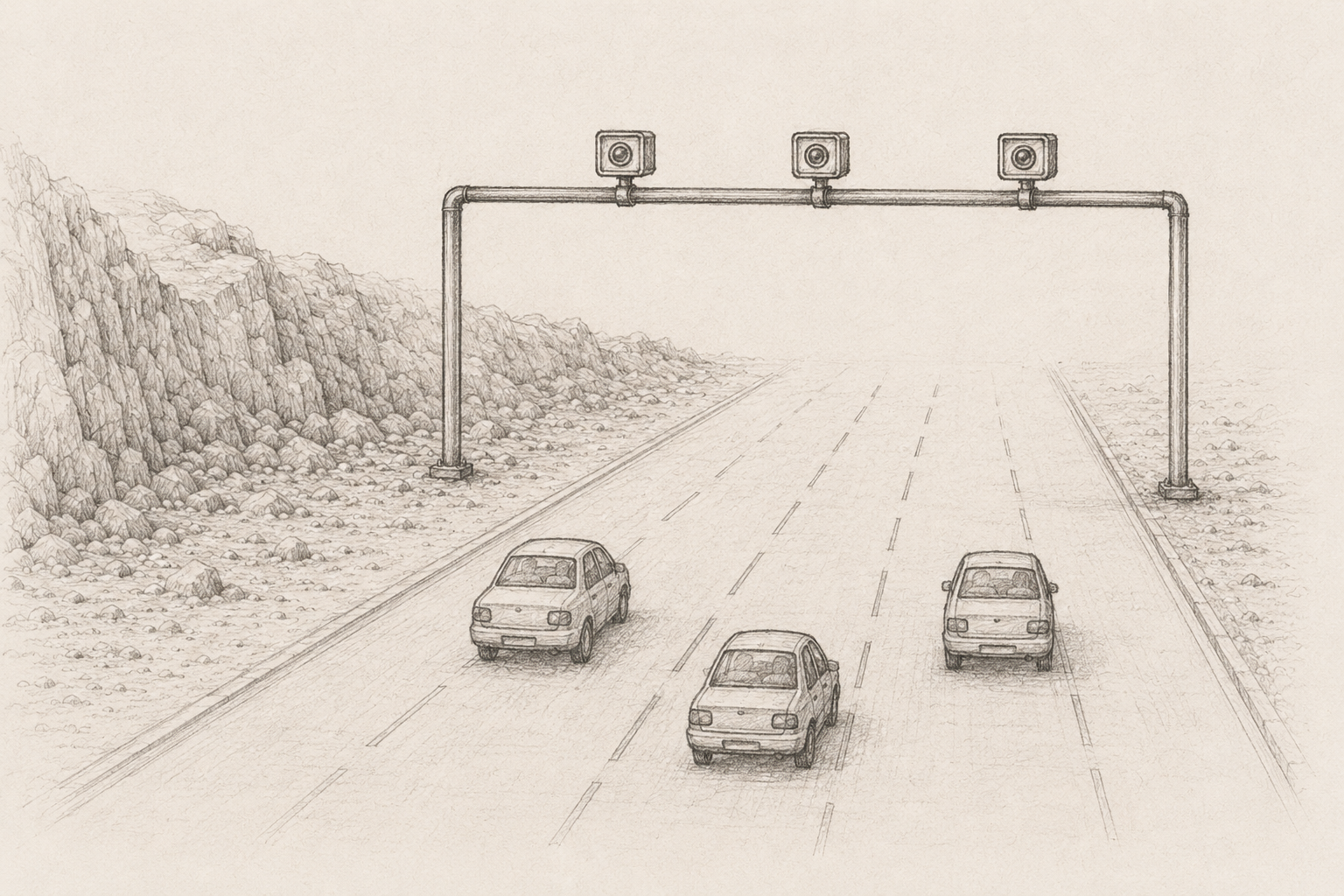
IP context, autonomous-system reputation, residential vs. data-center routing, and impossible-travel velocity. The layer that catches the cheapest automation before it lands.
Track 03 / 08 Layer III
JA3/JA4 TLS prints, HTTP/2 frame ordering, TCP fingerprints, and header shape. Verdicts you can ship before a single line of JavaScript runs.
Track 04 / 08 Layer IV
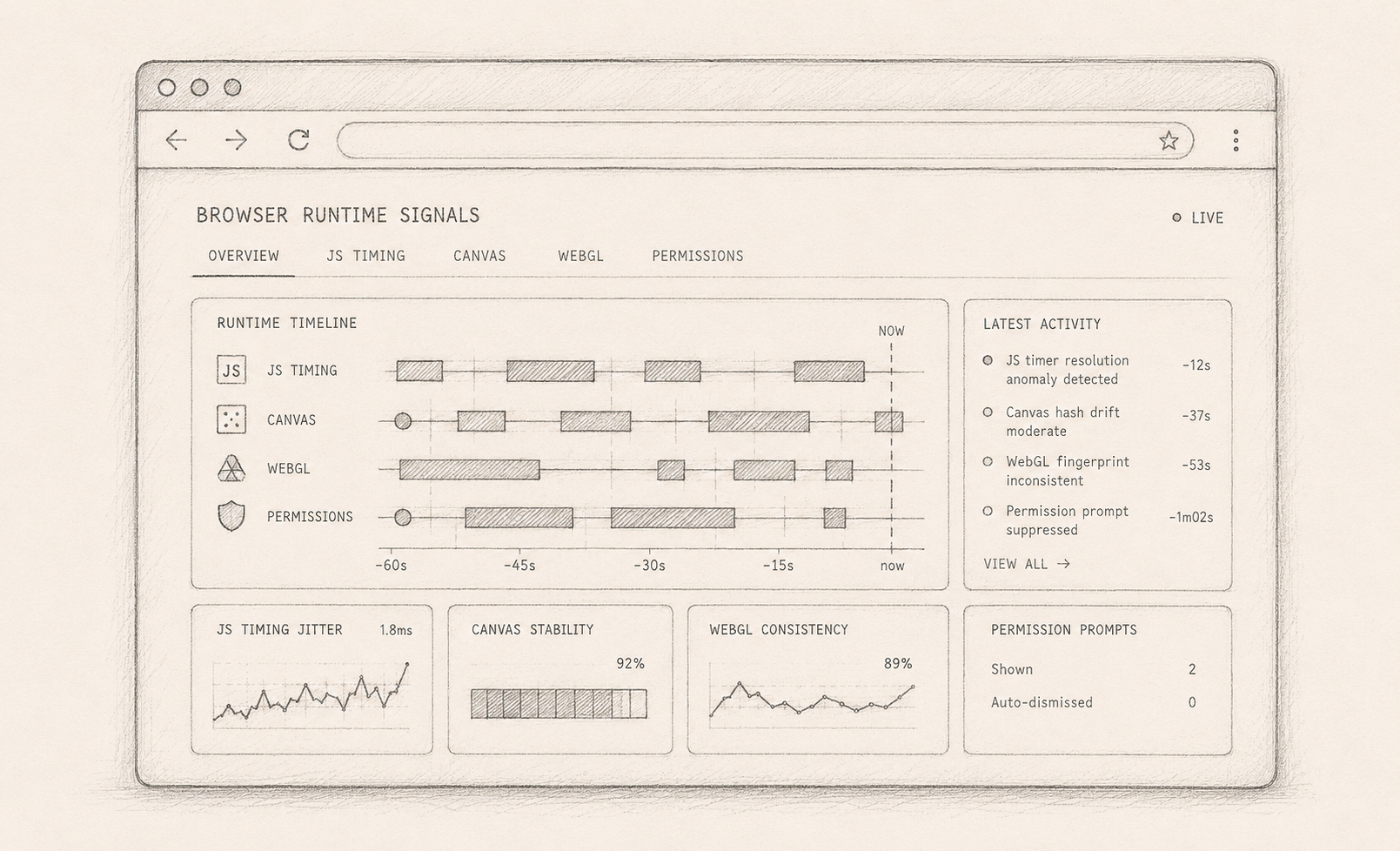
JS timing, Canvas and WebGL fingerprints, and permission-prompt behavior. The rich runtime evidence that exposes stock automation and most anti-detect patches.
Track 05 / 08 Layer V
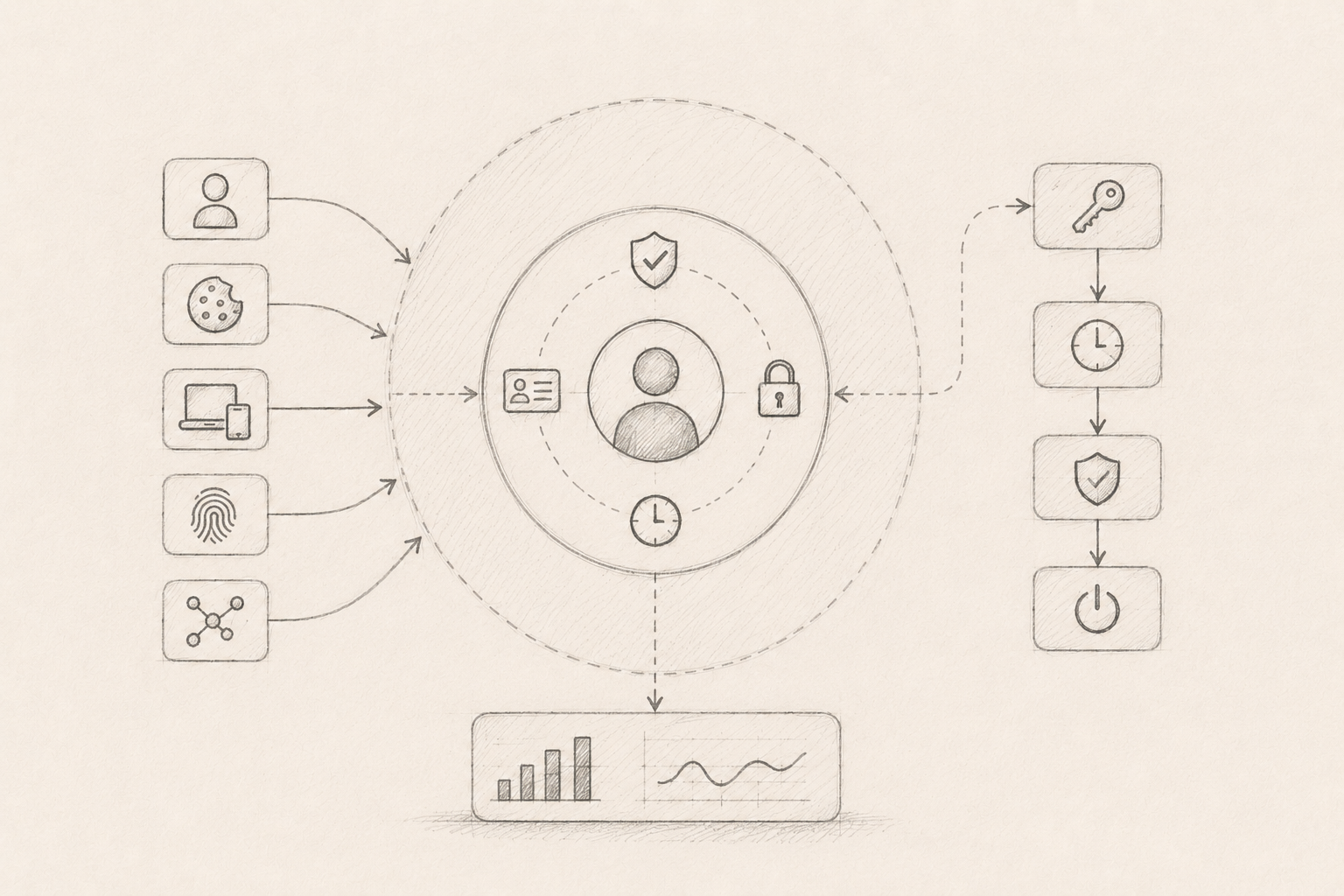
Stitch fingerprint, cookie age, account graph, and session lineage together so spun-up accounts cannot pretend to be returning users.
Track 06 / 08 Layer VI
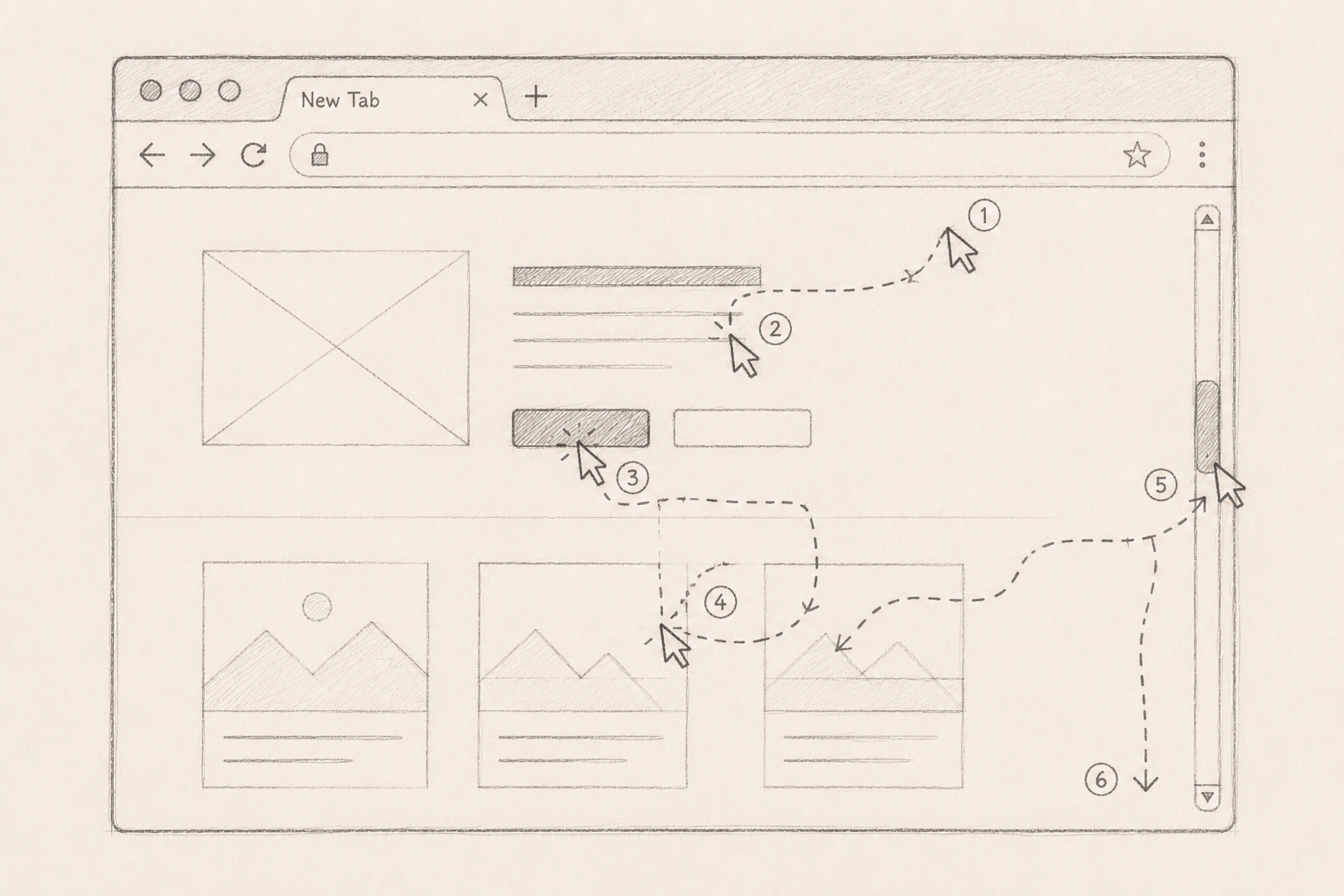
Turn mouse, keyboard, scroll, and dwell traces into features, models, and explanations that respect real-user variance instead of fighting it.
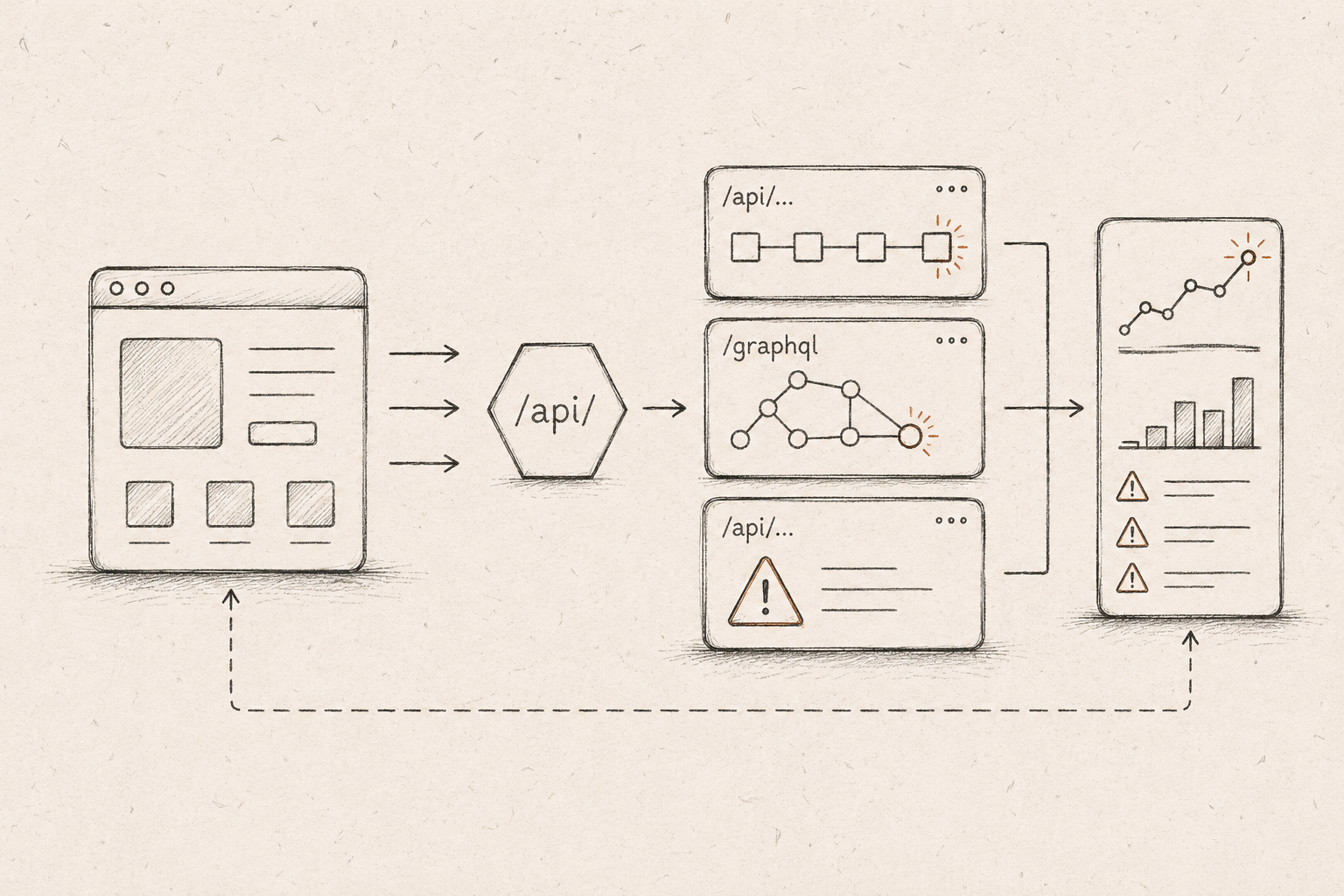
Track 07 / 08 Layer VII
Watch endpoint order, GraphQL query shape, and error patterns. This is where automation reveals itself as a thing gaming the app rather than using it.
Track 08 / 08 Layer VIII
Translate signals into the cost of fraud, scraping pressure, review-queue load, and the false-positive risk the brand will actually accept.

Sandboxes · BLS-03
Controlled environments for testing detections, challenges, thresholds, and evasion hypotheses before they touch production traffic.
Sandbox 01 SBX-01
Replay synthetic traffic cohorts to see how fingerprint, IP, timing, and session signals shape a verdict.
Sandbox 02 SBX-02
Insert challenges into controlled journeys and measure where useful evidence becomes real-user friction.
Sandbox 03 SBX-03
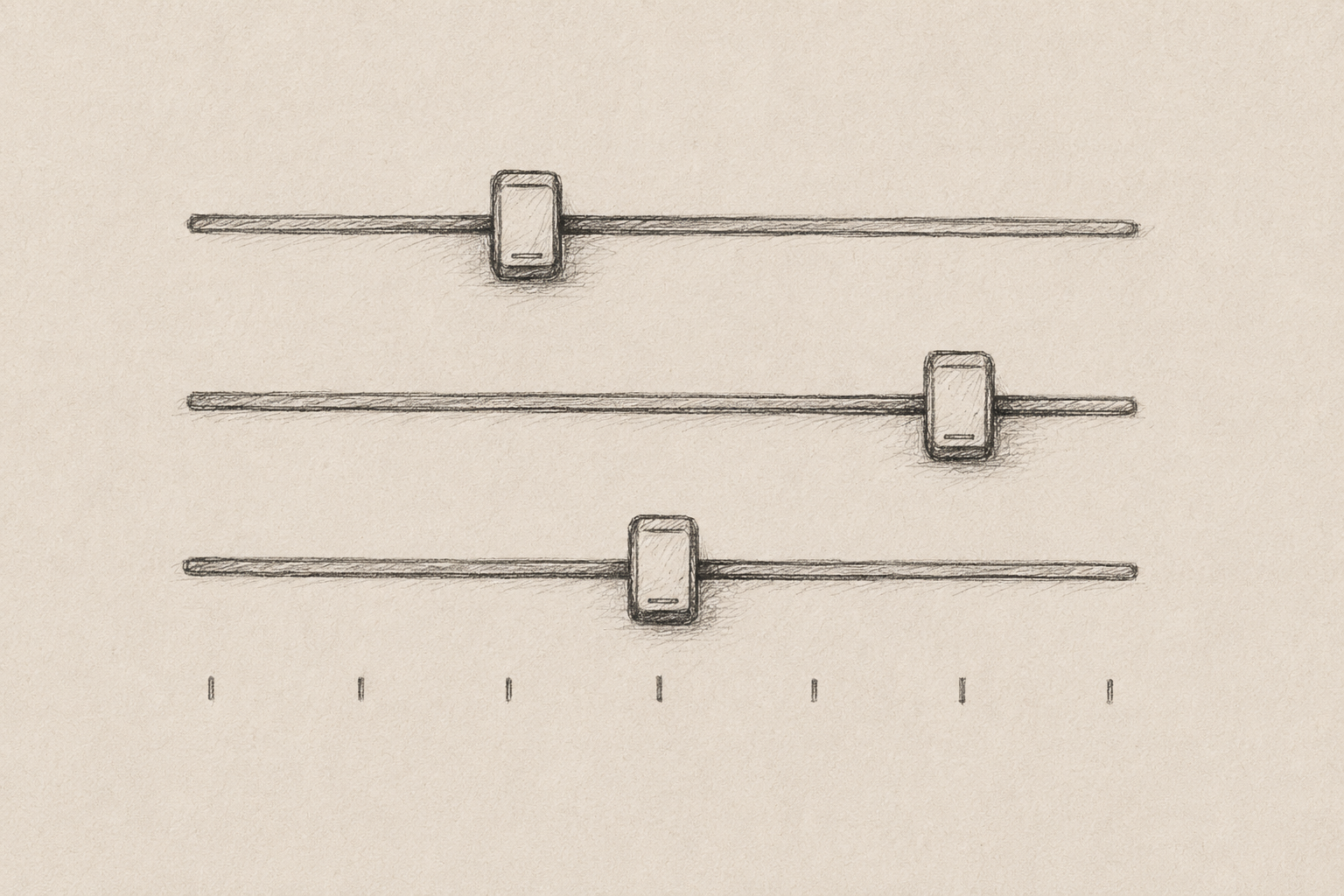
Tune thresholds against abuse pressure, false-positive cost, review volume, and operator confidence.
Sandbox 04 SBX-04
Review spoofed profiles, replay traces, and coherence checks in a contained defensive environment.